Maintaining website security nowadays is very challenging work. Your entire work can be gone by a website vulnerability. In this article, we tried to shed some light on website security general concepts. Also, we tried to create a list of how can you protect your website?
What is Website Security?
Website security is a process or action through different methods that protect your website from being hacked or damaged. It means protecting your website from vulnerabilities and outside exploitation.
Website Security Importance?
Every day almost 50000 websites got hacked by a rough estimate. These numbers are growing almost hourly. Thus, it is very crucial to make your website secure.
Over 50% of all internet traffic sources are now automated tools like bots, hacking tools, scanners, spammers, and impersonators. These tools and cybercriminals are always trying to find out loopholes in your website.
We need to be proactive to secure your website from outside attacks. You can lose a lot if your website got hacked. You could lose your reputation, brand value, and customer information. Cybercriminals can exploit the vulnerabilities of your website and can cause financial loss to you and your customers. Also, it is very much expensive for a hacked website to clean up its mess. Strong website security measures can keep your website safe from hackers and hassle-free.
Why Websites Get Hacked?
Information and resources are the main two things hackers wanted. Cybercriminals use personal information to gain access to financial resources. By collecting information, they can hack into financial accounts and steal money. Also, they can use a website to redirect their visitors to another website for affiliate gain.
Hackers hack into computers, servers, etc. by using vulnerable websites’ backdoor and using the resources for their work. They can infect outdated software, plugins, and themes and use them for a criminal act.
Type of Website Security Threats
Spam
Spam commenting is common on websites. Your website’s comments section can be used for building backlinks. Visitors could get discouraged to comment and engage in your site if they saw spam commenting. Also, phishing links on the comment section can cause trouble for your visitors if they accidentally click those links.
In addition, search engine crawlers can detect malicious URLs in your comment section and penalize your website.
SEO Spam
SEO spam or Spamdexing is a technique of using a well-ranked website to promote or rank contents that would not rank otherwise. Hackers use this technique to promote their content and generate revenue. SEO spam can create havoc for any website. As Google considers this as black hat SEO, they can penalize the infected website. Sometimes google just ban the website from search engines.
Viruses and Malware
Website Malware (or malicious software) is typically a code or file, developed to harm a website and its visitors. A malware that self-replicates is called a virus. Stealing information, redirecting pages, taking over website control, disrupting website services, and infecting website visitors are some of the main targets of website malware.
There are thousands of variations of malware available in the cyber world, but the most commons are:
| Type | What It Does | Real-World Example |
| Ransomware | Disable data access, Want ransom. | Locky |
| Fileless Malware | Does not need executable files, Attack via legitimate programs |
The Dark Avenger |
| Spyware | Hide on device and steal sensitive information | ThreatsCoolWebSearch |
| Adware | serves unwanted advertisements | Fireball |
| Trojans | impersonate as harmless file and desirable code | Zeus |
| Worms | Replicates and spread through computers | Toxbot |
| Rootkits | malicious software gives unauthorized access | Olmasco |
| Keyloggers | monitor applications and give access to information | Olympic Vision |
| Bots | launches a broad flood of attacks | Echobot |
| Mobile Malware | infects mobile devices | Triada |
DDOS Attacks
Distributed Denial of Service (DDoS) attacks target websites and web applications. The main object of this attack is to make a website unavailable or slow for the target audience. To create a DDoS attack, attackers create fake traffics or connection requests by using botnet (multiple connected online devices). The huge amount of unwanted traffics overwhelm the targeted website or services, making it slow or crushed. Unlike other types of cyber attacks, DDoS does not target website security. Its main target is making any service unavailable.
Brute Force Attack on Website Admin Area
Brute force is a continuous attack on your website login credential, control area, or encryption keys. In this type of attack, attackers will try to break the security of a website by trying multiple combinations of usernames and passwords. If an automated lockout policy is not in place for a website, hackers might try to exploit the security of a website by creating a Brute force attack.
Code Injections
A hacker can inject malicious code through vulnerable SQL queries. Hackers merged their code with the query sent by a website. The changed code reached the database and if it is successful, it can reply with the information hacker wanted instead of the information needed by the website. Hackers can also change the database information by code injections.
Cross-site Scripting Attacks
Cross-Site Scripting (XSS) is a type of attack, where cybercriminals inject malicious scripts into a website to take it under control. The attacker can inject malicious scripts using the vulnerability of a target web application. Most commonly, JavaScript is used for this type of attack.
XSS allows an attacker to inject content into a website and modify the website. If a site administrator accidentally executes any malicious script while logged in, a hacker can get information from the website or even take control of the website.
Phishing Attacks
Sometimes hackers design and develop fake websites and pages to mimic the original. They do this to steal information from visitors who landed on the page thinking original. (Example: setting up a bank-landing page to steal personal information).
How to Keep a Website Safe?
It is always better to be proactive and prevent website security disasters rather than fighting after the disaster itself. It is also cheaper to activate security measurement than pay for the recovery of an infected website. We can do the following things to keep our website secure.
Installing SSL Certificate and Using HTTPS Protocol
SSL certificate is a technique of transmitting data from a host to a client using an encrypted connection. It is also known as a website security certificate. It changes a website from Hypertext Transfer Protocol (HTTP) to Hypertext Transfer Protocol Secure (HTTPS). HTTPS is more secure than HTTP. HTTPS uses a short-term session key to encrypt data. By installing an SSL certificate and using HTTPS protocol, a website can communicate with its visitors via a secured connection. It helps a website secure its data from being hacked. Data such as:
- Bank transaction and user personal information
- Patients’ medical records
- Login credentials etc
In addition, Google considers HTTPS as a ranking factor and improves search ranking.
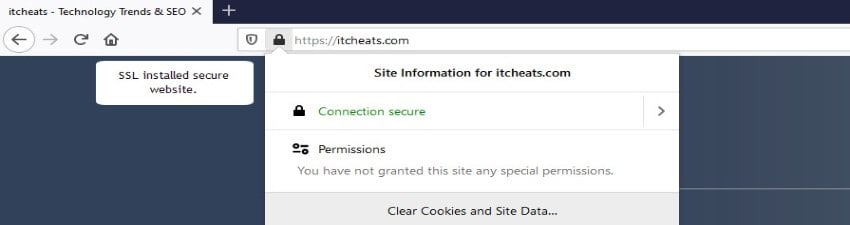
Website with an SSL certificate
Keep Software and Plugins Up-To-Date
Updating everything is necessary for website security. Developers always try to improve their software, plugins, themes, CMS, and codes. They try to fix any bugs or glitches by updating their products. These typically come with security improvements.
Hackers always try to find vulnerabilities of outdated software. Hackers scan websites for vulnerabilities and try to find a way to hack them. If a website is up to date with the latest software updates, it is not easy for cybercriminals to invade them.
Choose Web Hosting Wisely
Website security somewhat depends on the hosting provider and hosting plan. A website will get the same level of security measures as the hosting provider implemented on its servers. But there is a catch, if a website is hosted on a shared hosting plan with other websites, it can be hacked or attacked from the vulnerabilities of another website. If any website from a shared hosting got hacked, a hacker could have gained access to the hosting server. It means your website is not safe anymore.
VPS can be the solution to this problem. It will increase website security. If you are not short of money, you should go for a VPS plan. Also, you can try to choose a shared hosting plan from a reputed hosting provider.
Having Strong Login Credentials or Password
Compromised passwords or admin credentials are one of the causes of a website security breach. Cybercriminals often try to steal the login credentials of a website and then access the website as an admin. They can steal payment information, user information, and other website data if they have access. They can use the website for a false post or other unethical advantages also. Having a strong and secure password can prevent this type of data breach.
Password usage best practice:
- Change your password regularly (every 3 or 6 months). Make it unique and do not reuse it. You can use a password manager for this purpose.
- Create a strong password. Use special characters. Do not use random words on your passwords. These are easily crackable. You can use a password manager to generate a long and unique password.
- Use two-factor authentication to be more secure.
Keep Your Personal Devices Secure
Keep your computer, tab, or phone clean and secure. Cyber criminals can attack your website through your devices. They can steal your website credentials through any of your devices. To prevent this, install antivirus and malware software on all of your devices. In addition, browse safely from your devices.
Add Tools for Scan and Monitor Website
Monitoring website changes can be effective in securing a website. Scanning and keeping logs is a very effective way of finding out security issues. Triggers need to be set for brute force attacks or DDOS attacks.
Scanning, reviewing, and keeping an alerting mechanism can be crucial for blocking cyber attacks. Every website needs to implement scanning and monitoring tools for this purpose. Website security scan can be done free by using the following tools:
Check User Access and Permissions
Most of the time it is a human mistake that makes a website unguarded to cyber-attacks. If too many people have access to a website, it could lead to cyber security issues.
We can solve this problem by giving website access to limited users. Also, divide the access system by work type and grant access to people by work requirement and for a limited time. We need to make sure that each user has their credentials and does not share credentials.
Do not give access to an outside developer to change the setting of your website. Only give them the least access for work to complete.
Website Backup
Your website can get hacked at any time and may need to restore from a previous version. If you have your website backed up regularly, you can just replace the compromised version with a backed-up version.
For WordPress, we can use a plugin called “UpdraftPlus” for backup and restore. Otherwise, we can use FTP software like Filezilla or try web hosting cPanel.
CMS Settings Configuration
Do not keep default settings for your CMS website. Hackers can exploit the default settings of your website. Change file permission settings, comments settings, user access settings, login settings, etc.
Precautions for File Uploads
Sometimes we allow visitors to upload files on our website. But this can be dangerous. Hackers can upload malicious scripts or executable files. They can then use loopholes created by the uploaded file.
We can set up our website in a way, that any file uploaded by visitors should be stored on a different server. Third-party software like Filestack can help to upload files securely. And always use those files after scanning for viruses and malware.
Keep Website Clean
Keeping a website clean means deleting unused files. It applies to applications, databases, plugins, themes, etc. Organize the file structure of your website to keep track of changes.
Web Server Security
Limit access to root files. Server configuration files allow executing server rules. So, it is very important to keep these files safe from outside attacks. We can create some rules to keep the root directory from browsing. CMS configuration files, admin areas, etc., should be locked down.
Best Practices Personal Security
Scan your computer for malware and viruses periodically. Malware tends to spread through different devices by using text editors and FTP clients. Remove all pirated, cracked, or unused applications from your devices. Cracked software is one of the main transfer methods of malware and viruses.
Website Firewall
A website is not always 100% secure with an SSL certificate installed. Hackers can get your website data, or take control of your website by using web application vulnerability. Hackers can attack your website using DDoS. They can slow it down or take it down. Websites can prevent these attacks by using a firewall application.
How to Recover a Hacked Website?
We can take all the precautions and measures we can think of, but the thing is a website can get infected in a thousand’s ways. And we cannot prevent a website from being hacked 100%. What we can do is try not to be hacked. And if we got attacked, do certain things to clean the website.
Scan Everything
Firstly, we need to scan the website and the local setup for outside intrusion. For scanning websites, we can use web-based applications or crawlers. We can try multiple scanners to look for different types of invasions.
For local setup (i.e., notebook, desktop, tabs, etc.), it is important to scan for viruses, malware, or Trojans. Most of the time the source of website attack is your local setup. To prevent this, you need good antivirus and malware solutions.
Clean Malware from Website
If your website got hacked, you need to check it for malware presence. You need to clean your website thoroughly. A website needs to be free a hundred percent from malware. If it is not, the site can get hacked repeatedly. You can remove malware from your website manually or using paid services.
Update Website Applications
We have already talked about the importance of updating websites applications. It helps to keep a website’s vulnerability at a minimum. For a compromised website, updating every aspect of the website is one of the solutions.
Review Admin Access
We need to review the admin section. If any unusual user is found, we need to remove those immediately. Hackers can get access to the admin area by using malicious code. We need to clean malware from the website. Also recheck for any unwanted user.
Resetting all-access might be a good step for this scenario.
Change Login Credentials
Changing login credentials for a compromised website is a must. You also need to change the login information for other services, linked with your website. If your website is compromised, the basic idea is to replace every password.
Secure Hosting Provider
A shared hosting server has a greater risk than a dedicated server. In shared hosting, there can be more than one website hosted. If any of the websites got attacked, the shared server might get compromised also. A shared server needs to be free of viruses for a website to be hosted again.
Using Backup
We have already discussed website backup. If we failed to clean up the website from malicious code, we can restore a previous clean version of it.
Website Security Tools
There are different types of website security tools. Some are free and some are not. And some are partially free. Here we are mentioning some of them in no particular order.
Sucuri
It is a malware and security scanner. You can check your website for free here. Also, they provide paid services to fix a hacked website.
Qualys
SSL server test of Qualys analysis the configuration of the SSL web server. It provides an in-depth summary of your website SSL.
SiteGuarding
It can check for website blacklisting, malware, spam blacklisting, and many more.

SiteGuarding Scan
There are several other tools available for website security checks. Such as
We hope that with the help of this article we can create some awareness about website security.



Hi, I think the overall post is good but if you could include more real life images and examples it could be better.
Whats up very cool web site!! Man .. Excellent .. Amazing .. I’ll bookmark your blog and take the feeds also…I’m happy to find a lot of helpful info right here within the put up, we need work out more techniques on this regard, thanks for sharing. . . . . .